- By ACI
- 05 March, 2026
- 7 min Read
HIPAA-Compliant Healthcare Software Development: Security Architecture Beyond Checklists
Healthcare executives and insurers understand that HIPAA compliance goes far beyond documentation. It is about protecting patient trust, preventing costly breaches, and ensuring that healthcare technology systems can withstand both regulatory scrutiny and modern cyber threats.
Healthcare organizations today operate in an environment where clinical systems, cloud infrastructure, and third-party integrations constantly exchange sensitive patient data. In this landscape, compliance must be built directly into the technology infrastructure.
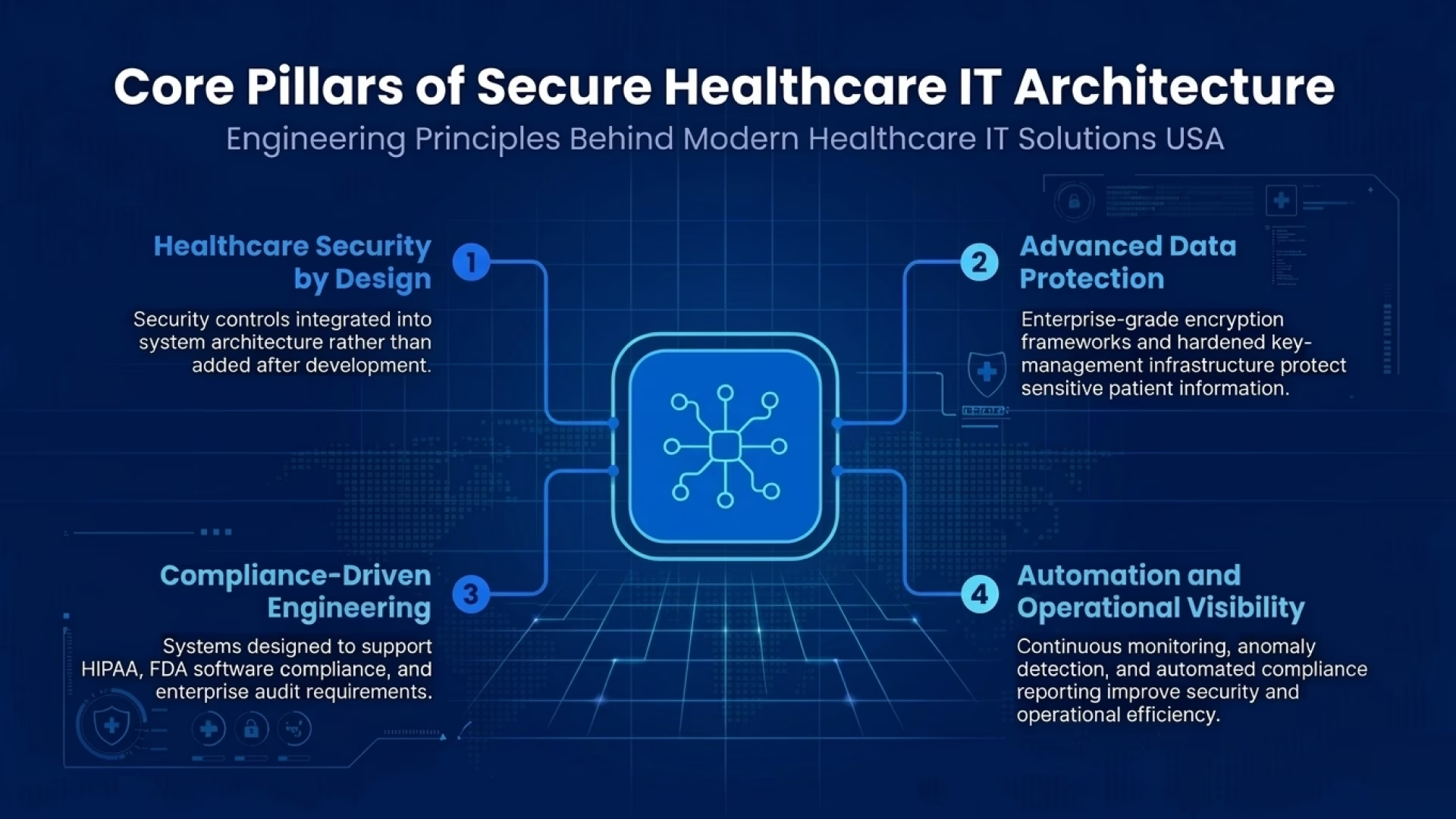
Aryabh Consulting approaches this challenge through architecture-driven Healthcare IT Solutions USA, where security controls are embedded into the engineering foundation of the software itself. Encryption frameworks, role-based access controls, audit integrity systems, zero-trust security models, and intelligent automation work together to create resilient healthcare platforms.
Security practices are integrated across the entire development lifecycle, including threat modeling, secure coding standards, rigorous testing, and controlled deployment pipelines. This approach ensures that compliance is maintained from system design through production deployment.
Compliance Requires Architecture, Not Just Policy
HIPAA defines the regulatory standards for protecting electronic protected health information (ePHI). However, the effectiveness of those rules depends largely on how healthcare systems are engineered.
Healthcare data breaches are expected to cost organizations an average of $7.42 million per incident in 2025, including legal costs, recovery expenses, and regulatory penalties.
Documentation alone cannot prevent these losses. Effective healthcare technology infrastructure depends on technical safeguards such as strong encryption, strict identity management, continuous monitoring, tamper-resistant logging, and secure interoperability across systems.
Organizations increasingly recognize that Healthcare IT Solutions USA providers must engineer compliance into system architecture rather than attempting to retrofit security during audits.
Building Secure Architecture Before Development Begins
Many security incidents originate from poorly designed legacy systems. Research shows more than 80% of healthcare breaches involve configuration weaknesses or outdated infrastructure.
For this reason, Aryabh Consulting begins projects with a structured security and healthcare consulting assessment. The process evaluates several critical areas:
- Data flow pathways across applications
- Integration dependencies between systems
- Identity and access management gaps
- Regulatory exposure points
- Infrastructure risk factors
Understanding these elements early ensures healthcare IT systems are designed with security controls embedded at every layer.
Encryption as the Foundation of Healthcare Data Protection
Encryption remains one of the most effective defenses against unauthorized access to patient data. Yet misconfigured encryption continues to cause significant security incidents. In 2024, nearly 65% of hospital data breaches were linked to weak or improperly implemented encryption controls.
Modern healthcare platforms protect sensitive information using enterprise-grade encryption frameworks. These typically combine AES-256 encryption for data at rest with TLS 1.2+ protocols for secure transmission across networks.
Encryption keys are managed through hardened key-management systems that control lifecycle access and prevent unauthorized retrieval. Together, these measures form the foundation of secure healthcare data infrastructure.
Managing Access and Reducing Insider Risk
Data security is not limited to defending against external attacks. Internal misuse of information remains a persistent concern across healthcare organizations.
Studies estimate that approximately 10% of healthcare breaches originate from individuals inside the organization.
To reduce this risk, Aryabh Consulting applies Role-Based Access Control (RBAC) within enterprise healthcare platforms. Access privileges are aligned with job responsibilities so users can only view or modify the information necessary for their work.
Additional governance controls include privileged access monitoring, segregation of duties for sensitive operations, automated user provisioning, and multi-factor authentication. These mechanisms strengthen healthcare data security while supporting regulatory compliance requirements.
Audit Integrity and Tamper-Resistant Logging
Healthcare organizations must maintain accurate records of system activity for regulatory reviews and incident investigations.
Advanced healthcare IT systems therefore implement tamper-resistant audit logs that capture authentication events, data access activity, configuration changes, and security alerts. Because these records cannot be altered without detection, they provide reliable evidence during compliance audits.
To further strengthen audit integrity, Aryabh Consulting Inc. applies blockchain-inspired verification techniques. These mechanisms create tamper-evident records that help validate log authenticity and maintain a transparent security history across enterprise healthcare environments.
Zero-Trust Security for Modern Healthcare Networks
Custom software development comes with real benefits but also challenges every business should weigh before making the investment.
Healthcare networks have expanded rapidly with cloud infrastructure, remote clinical access, and third-party data integrations. In this environment, traditional perimeter-based security models are no longer sufficient.
By 2025, nearly 75% of healthcare cyberattacks bypassed traditional network defenses, highlighting the need for stronger security frameworks.
Zero-trust architecture addresses this challenge by requiring verification of every user and device attempting to access the system. Within modern Healthcare IT Solutions USA, this model includes strict identity validation, continuous user behavior monitoring, network segmentation, and controls that prevent lateral threat movement.
These safeguards are particularly valuable for healthcare organizations operating hybrid cloud and multi-facility environments.
Automation Strengthens Operational Security
Healthcare IT environments generate enormous volumes of operational data, making manual monitoring inefficient and error-prone.
Research indicates that manual compliance processes contribute to nearly 30% of operational delays in healthcare IT operations.
To address this challenge, Aryabh Consulting integrates Python-based automation frameworks into secure healthcare platforms. These systems monitor logs continuously, detect anomalies, trigger alerts, and generate audit-ready compliance reports.
Automation allows healthcare organizations to maintain real-time visibility into system activity while reducing administrative overhead.
Secure Interoperability and EHR Integration
Modern healthcare delivery depends on reliable information exchange between hospitals, laboratories, insurers, and care providers.
However, interoperability failures contributed to approximately 25% of HIPAA penalties in 2024, often due to insecure integrations or weak access controls.
Aryabh Consulting addresses these challenges through secure EHR integration frameworks that support standards such as HL7 and FHIR. Secure API gateways, encrypted data pipelines, and structured permission layers help ensure patient information can move safely between systems.
These capabilities are a critical component of modern Healthcare IT Solutions USA, where data sharing must occur without compromising privacy or regulatory compliance.
Building Resilient Healthcare Technology Platforms
Healthcare organizations require technology partners who understand regulatory complexity, cybersecurity threats, and the operational demands of large clinical systems.
Through architecture-driven Healthcare IT Solutions USA, Aryabh Consulting develops enterprise healthcare platforms that combine secure infrastructure, interoperability frameworks, and compliance automation.
For healthcare executives and insurers, sustainable compliance depends on systems engineered for security from the beginning. This engineering-first approach helps organizations protect patient data while maintaining reliable and efficient healthcare operations.
Frequently Asked Questions
1. How does Aryabh Consulting go beyond basic HIPAA compliance??
We use encryption, role-based access, zero-trust architecture, immutable audit logs, and automation directly in the system design. Compliance is built into the foundation.
2. Do you use blockchain in healthcare security?
Yes. We apply blockchain-backed concepts to strengthen the audit trail integrity and avoid the unauthorized modification of the access records.
3. How do you automate security monitoring?
We use Python-based automation to monitor logs, detect anomalies, get alerts, and produce compliance reports in real time.
4. Can you support large hospital networks and insurers?
Yes. Our EHR solutions for healthcare enterprises and Healthcare IT solutions USA are designed for multi-facility health systems and insurers.
5. How do you ensure secure interoperability across systems?
We use encrypted APIs, healthcare interoperability standards, role-based permissions, and secure EHR integration frameworks to protect the data during the exchanges.